IT-School
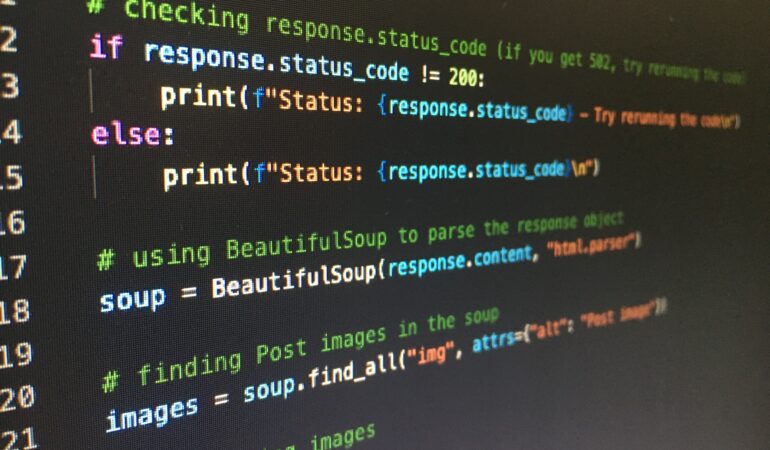
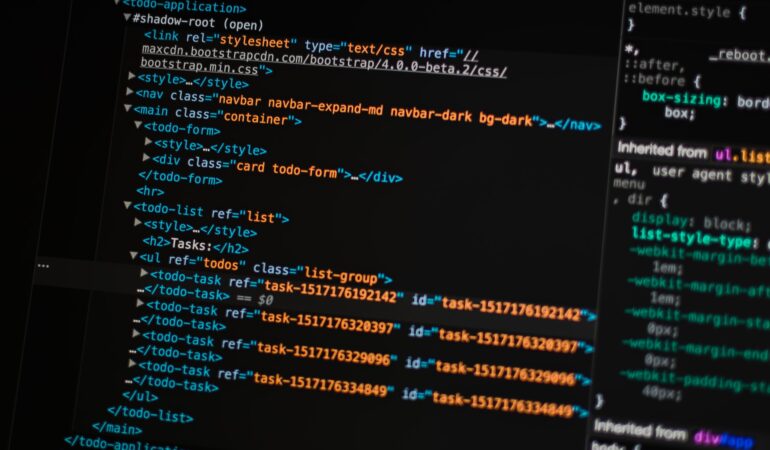
Front End
Developing
Sign up for consultation and testing, get a personalized development plan in IT
Stop procrastinating
it's time for action!
Get Started Now
We'll teach you everything from scratch and
help you get your first job-offer
IT-School
You will love your
profession!
Teachers with many years of experience will show the benefits of studying in the IT field. The training is built around real tasks that IT professionals are facing nowadays.
Sign up for a trial lesson



Our
values
QUALITY
Teachers with many years of experience in the field of IT teach the material in such a way that you get a confident start for work and development. IT courses at PeaPod are qualitatively different from all others in Mykolaiv: we create conditions for self-realization and personal growth.
SELF-DEVELOPMENT
Our teachers work every day to improve their knowledge and skills to teach you only relevant professions. We teach you to use modern technologies to achieve success in life.
RESPONSIBILITY
The IT school team takes full responsibility for its vocation - to teach children and adults.
Relevant education for those who want to learn a new
high-paying profession
Your future
teachers
are the strongest practitioners with diverse experience, they know how organized business nowadays, know the demands and demands of the labor market.
Join UsWe will help you
to feel freedom!
Not everyone has the opportunity to work remotely. IT specialists are one of the few who can boast of such an advantage. By learning IT technologies, you automatically become a free person. We will teach you to destroy visible and invisible boundaries.
Together with the specialist you will analyze your competencies, determine career goals and positioning in the labor market.
Get StartedTogether with a career manager, you'll put together a quality resume and cover letter that will help you stand out from other candidates.
Learn MoreThe employment manager regularly informs course students about current vacancies at our partner companies.
Read MoreSee what our customers
are saying...


As they say, I saw, understood and learned! Price-quality! Money well spent! No bullshit! Everything is clear and to the point! ...
Merle Switzer / Front End Developer


Thank you very much, I enjoyed it all! The course was informative and interesting. I would especially like to mention the ...
Lillian Combs / Designer


I am grateful to the school and our super teachers for such an interesting and rich course, I liked everything. A ...
Carolina Davidson / Designer
Our Friends
 GetDevDone is a go-to white label eCommerce development partner for marketing agencies and store owners: Shopify, Magento, and WooCommerce development by certified professionals.
GetDevDone is a go-to white label eCommerce development partner for marketing agencies and store owners: Shopify, Magento, and WooCommerce development by certified professionals.
 NAKIVO backup delivers enterprise-grade data protection, ensuring your business’s resilience against threats.
NAKIVO backup delivers enterprise-grade data protection, ensuring your business’s resilience against threats.

Law firm call tracking is a crucial tool for legal practices aiming to optimize their client intake process and enhance overall efficiency. With law firm call tracking services, firms can accurately measure the success of their marketing campaigns by analyzing the number of incoming calls, identifying referral sources, and tracking the conversion rates of potential clients.

IT outstaffing company will help you close the issue with the availability of experienced blockchain developers.

YouTube to MP3 app that we use to convert videos to audio format.

Join the international community of IT professionals with Anywhere Club. Expand your opportunities in the IT industry to work, study, and relocate to other countries.

Are you looking for mobile app developers for your medical startup? Topflight provides healthcare app development services with solid niche expertise.
1300
Students
80
Teachers
324
Projects
79
International Awards
Latest news &
insights
This course is designed for people who have knowledge of HTML, CSS and basic knowledge of the JavaScript programming language.The course ...
A course for beginners who want to learn Python and learn how to use it to create complex programs and solutionsThis ...
This course is designed for beginners who want to learn or improve their knowledge in web development.Front-end developer is one of ...